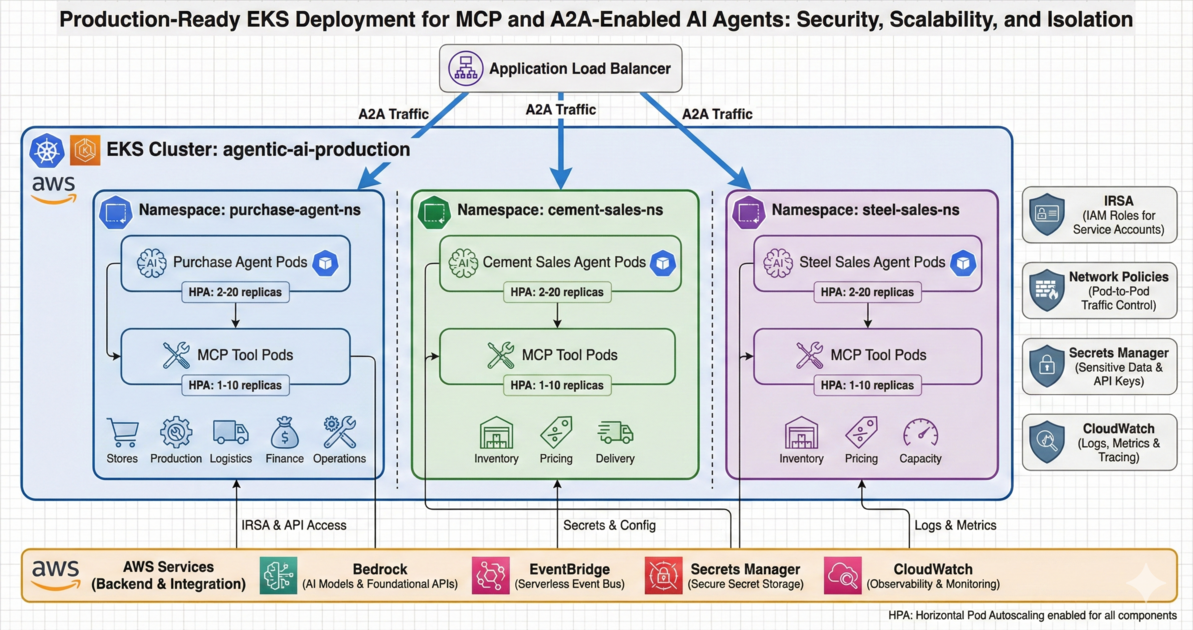
Deploying Agentic AI with MCP and A2A Capability on Amazon EKS
In-Short
CaveatWisdom
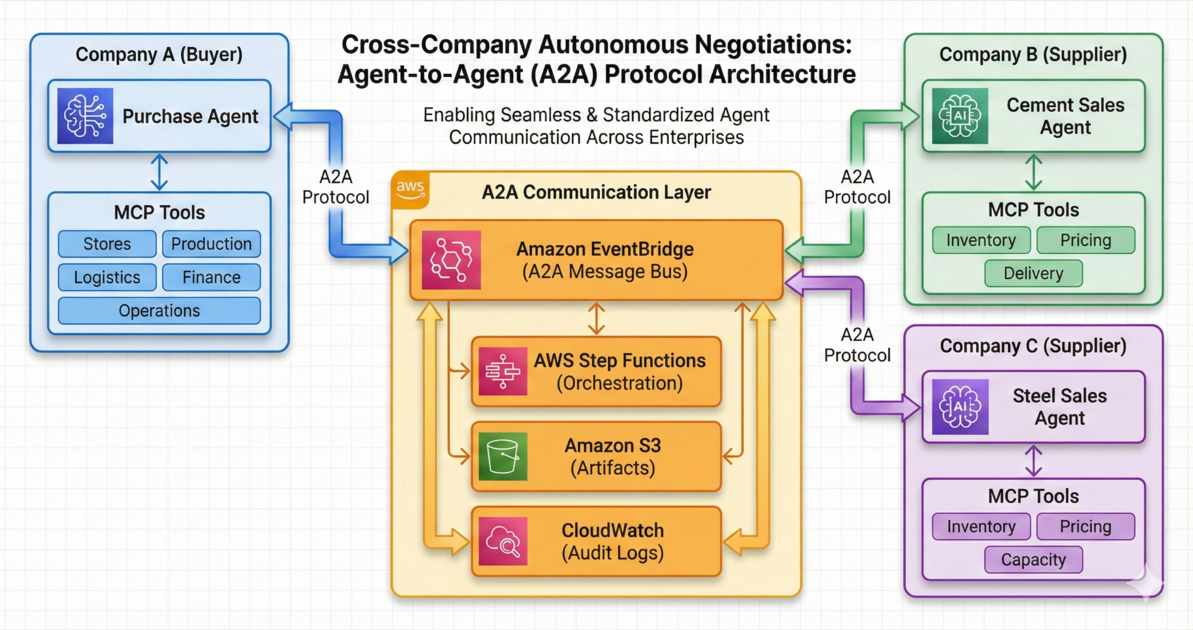
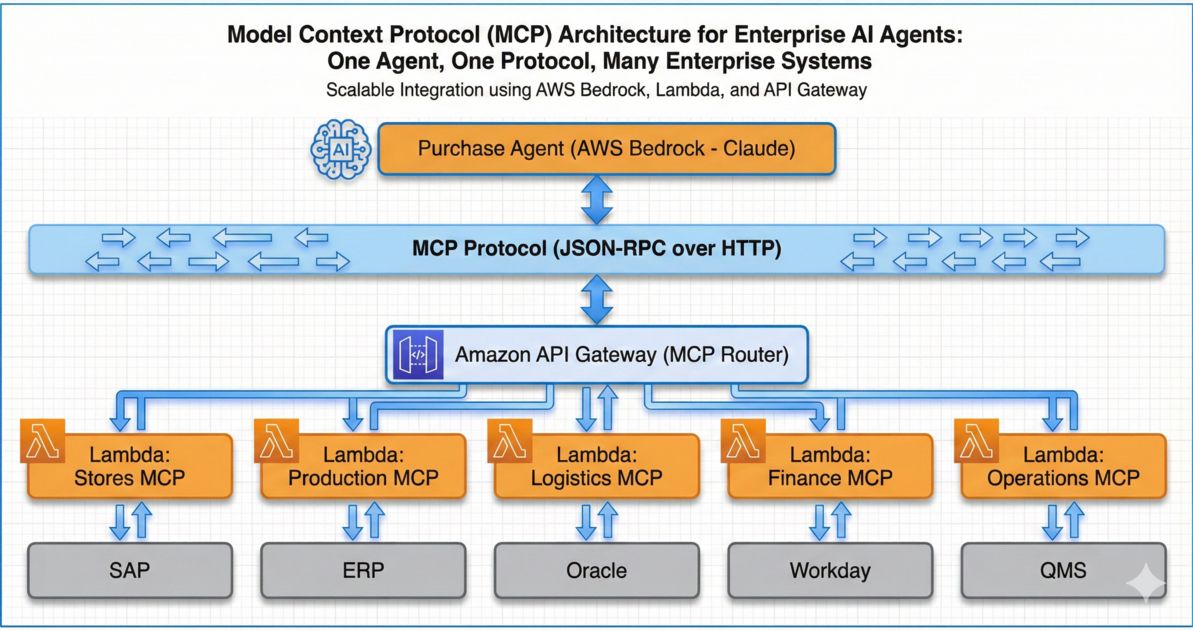
Caveat: You’ve built intelligent agents with MCP tools (Post 1) that communicate autonomously via A2A (Post 2). But deploying them without proper orchestration creates disasters: exposed credentials in containers, inability to handle load spikes when 500 RFQs hit simultaneously, no isolation between agents and MCP tools leading to security breaches, and operational nightmares with manual scaling. Ad-hoc deployments work in development but create security vulnerabilities and scalability bottlenecks in production.
Read More →