Best Practices in Implementing Security Groups for Web Application on AWS
In-Short
CaveatWisdom
Caveat: Its easy to assign source as large VPC wide CIDR range (ex: 10.0.0.0/16) in Security Groups for private instances and avoid painful debugging of data flow however we are opening our systems to a plethora of security vulnerabilities. For example, a compromised system in the network can affect all other systems in the network.
Wisdom:
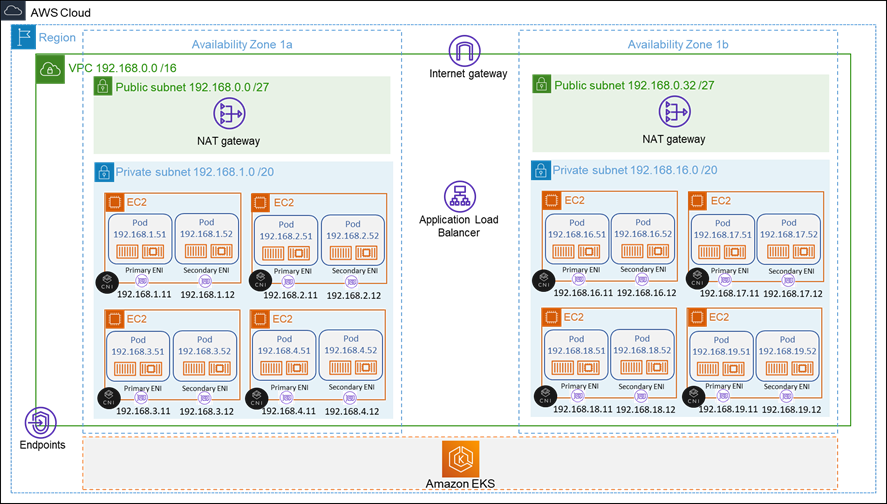
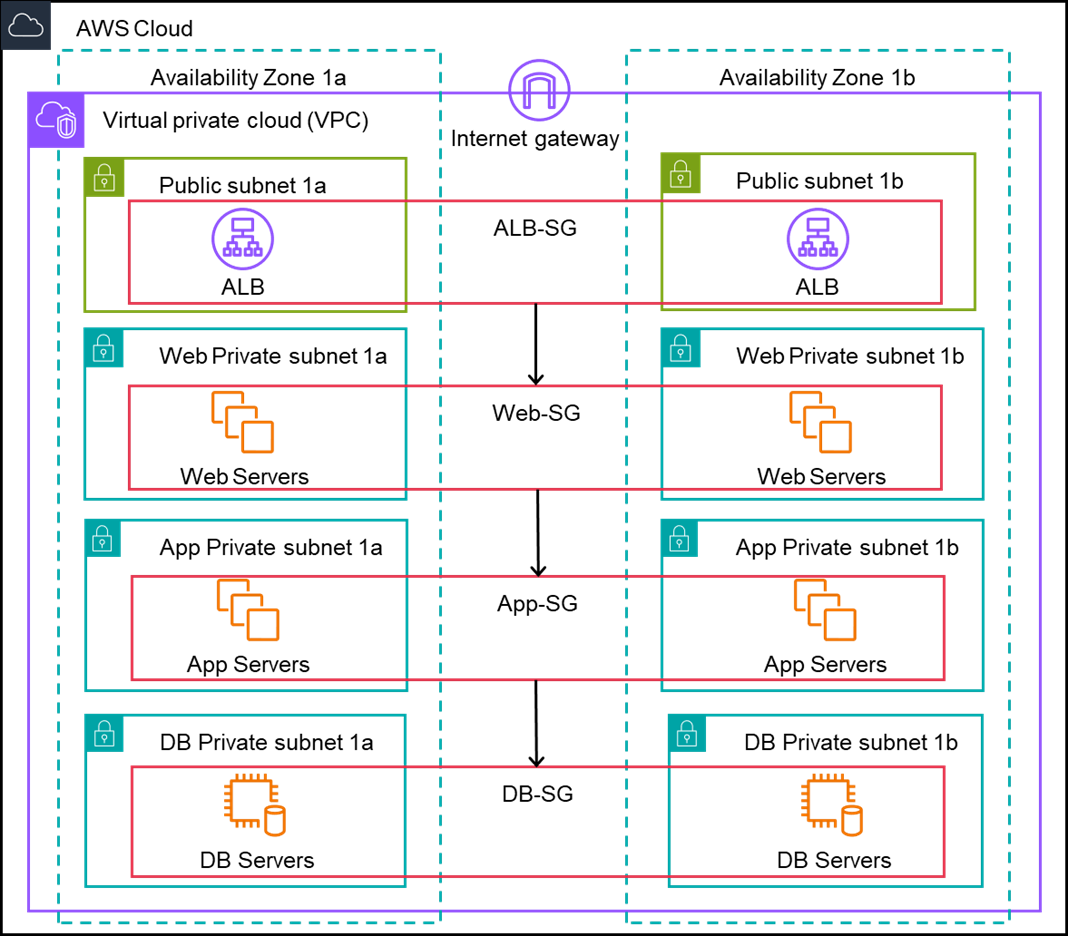
- Create and maintain separate private subnets for each tier of the application.
- Only allow the required traffic for instances, you can do this easily by assigning “Previous Tier Security Group” as the source (from where the traffic is allowed) in the in-bound rule of the “Present tier’s Security Group”.
- Keep Web Servers as private and always front them with a managed External Elastic Load Balancer.
- Access the servers through Session Manager in the System Manager Server.
In-Detail
Read More →